Secure WordPress - Improve Security with .htaccess + Firewall
 How can WordPress be protected from hacker attacks in the simplest and most effective way? There are already many comprehensive articles and different approaches on the topic of WordPress security and how to secure WordPress. This article is about achieving significantly more security with minimal effort.
How can WordPress be protected from hacker attacks in the simplest and most effective way? There are already many comprehensive articles and different approaches on the topic of WordPress security and how to secure WordPress. This article is about achieving significantly more security with minimal effort.
This blog post is intentionally kept brief. Anything that offers little benefit, is too complicated, or is hardly feasible without expert knowledge has been deliberately left out.
WordPress Security - Effective Measures for Enhanced Protection
To run WordPress securely, proper system maintenance is the most important factor. Regular updates, especially installing security-critical updates as quickly as possible, are clearly the top priority. Someone should always keep an eye on it.
Secure WordPress - what does that actually mean?
Before we get to the advanced security measures, here is a brief summary of the basics:
- Strong passwords (admin account, FTP/SSH, database, hosting control panel).
- Enforce HTTPS/SSL for the entire site.
- Install as few plugins and themes as possible (delete unused ones).
- Only obtain themes and plugins from secure/original sources.
- Regular backups (e.g. via 'UpdraftPlus Backup Plugin').
- A secure hosting environment.
- Multiple WordPress instances should absolutely be isolated, each running under its own system user (-> prevents mass hacks).
Basic hosting packages where this separation is not possible are unsuitable for hosting multiple sites.
- Multiple WordPress instances should absolutely be isolated, each running under its own system user (-> prevents mass hacks).
- Secure devices used to access the website.
Beyond these basic points, the following measures have proven effective for more advanced hardening.
1) Add to the .htaccess file in the main directory
When it comes to security, the power of the .htaccess file is unmatched. It can be used to block individual file calls and even lock down entire directories.
In the root directory, you can extend the .htaccess file as follows so that only the PHP files that require direct access can still be called.
# Blocks all *.php requests except index.php and selected core files in the document root.
# The subdirectories (wp-admin|wp-content|wp-includes) are not affected.
RewriteEngine On
RewriteCond %{REQUEST_URI} !^/(wp-admin|wp-content|wp-includes)
RewriteCond %{REQUEST_URI} !^/(index|wp-login|wp-comments-post|wp-cron|wp-trackback|xmlrpc)\.php
RewriteRule ^(.*\.php)$ - [R=403,L]
2a) Protection via .htaccess - Secure wp-content
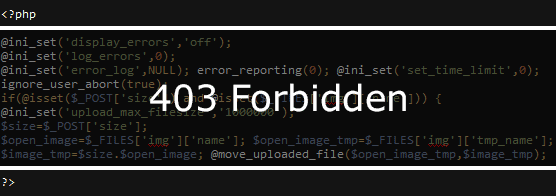 This makes especially good sense for the highly dynamic and extensive /wp-content directory. Injected PHP code and backdoors are effectively shut down this way.
This makes especially good sense for the highly dynamic and extensive /wp-content directory. Injected PHP code and backdoors are effectively shut down this way.
Assuming a hacker had placed code at
https://www.webseite-bereinigen.de/wp-content/plugins/akismet/wrapper.php
a backdoor script, this file would not be accessible if the wp-content directory is protected (403 - Forbidden). The same applies to all other files located deep inside wp-content or injected there in any way.
In the past, there have been attacks exploiting plugin vulnerabilities that could even be completely blocked by .htaccess protection alone.
See WP File Manager and Contact Form 7 vulnerabilities.
The WordPress directory in general - secure wp-content
The .htaccess directives can simply be copied into a newly created file or into an existing file at /wp-content/.htaccess. In very rare cases, additional exceptions may be necessary. If anything is still missing here, please use the comment function below.
Protect the upload folder
The /wp-content/uploads folder can also be protected separately with its own .htaccess file. PHP files generally have no place there, so all .php requests should be blocked. The /wp-content/.htaccess already covers the uploads directory as well - but if it should ever go missing (for example, if it is deleted by accident), this extra layer of protection certainly does no harm.
2b) Nginx configuration for wp-content protection
The .htaccess concept is only supported by the Apache web server. Unfortunately, the Nginx configuration can only be adjusted with a few hosting providers.
3) Secure WordPress with a firewall (NinjaFirewall)
 As a highly effective and high-performance firewall, the plugin 'NinjaFirewall' is recommended. Unlike other solutions, there are no data protection concerns here - the firewall does not phone home. In addition, NinjaFirewall is one of the most performant firewalls because it does not fill the database with log entries, unlike Wordfence, for example.
As a highly effective and high-performance firewall, the plugin 'NinjaFirewall' is recommended. Unlike other solutions, there are no data protection concerns here - the firewall does not phone home. In addition, NinjaFirewall is one of the most performant firewalls because it does not fill the database with log entries, unlike Wordfence, for example.
New security rules are provided free of charge to all users. By default, it checks hourly whether updates are available that protect against new types of attacks.
Another useful feature is email notifications for pending security updates.
4) Secure the WordPress login - lock or hide /wp-admin & wp-login.php (optional)
Current WordPress hacks are often also linked to unwanted or stolen admin user access - logins via /wp-admin or wp-login.php followed by a malicious plugin/theme upload.
When it comes to adding extra protection to the WordPress login, you can either use NinjaFirewall's Login Protection feature (there is a menu item for it) or hide the login by simply changing the login URL.
Another solution for greater security is the still not widely established 2-factor authentication.
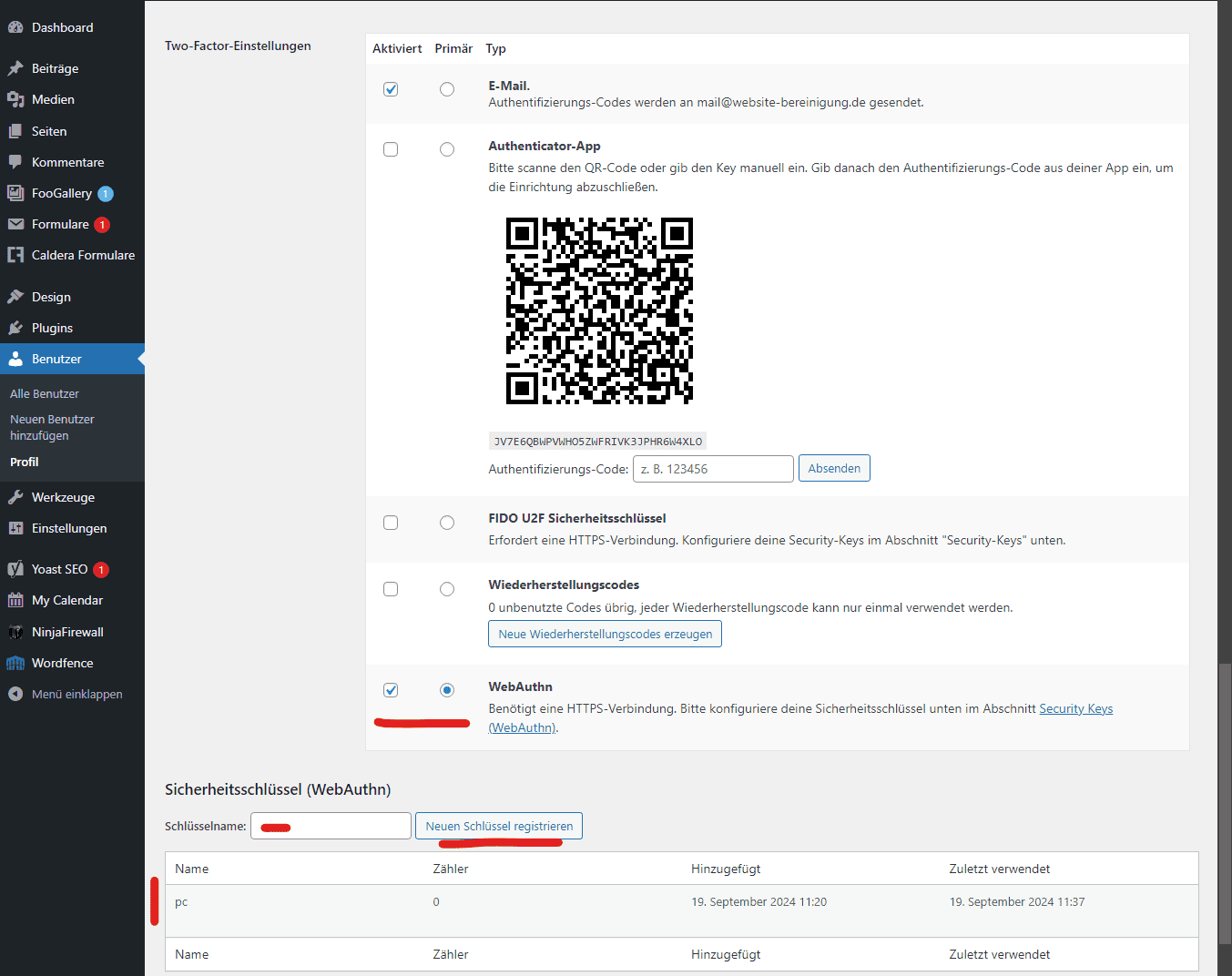
4a) Set up 2-factor authentication and enforce it for admin users

WebAuthn - passwordless login as a 2FA alternative
A modern way to log in without entering a password directly is the WebAuthn standard (a FIDO2 project of the W3C).
Instead of a password, Apple’s Touch/Face ID, Windows Hello (PIN, facial recognition), and Android’s biometric screen lock can be used here for authentication.
Once set up, the login method can be selected as the primary option in the user settings, enabling a fast, convenient, and secure sign-in experience.
WPS Hide Login
As a second option, it can definitely make sense to hide the login completely. Of course, this is less useful if there is a frontend login (such as the customer login in a shop).
The plugin 'WPS Hide Login' is a good choice for renaming the login. After activation, you can define a custom login URL under Settings -> General at the bottom of the page - /admin-in, for example.
As a result, wp-login.php and /wp-admin can no longer be accessed when logged out. Accordingly, login attempts via the standard URLs will no longer occur at all.
In many hacks in the past, plugins/themes were uploaded. Many logs show that access was gained via wp-login.php / wp-admin.
Weak passwords / privilege escalation / session hijacking or cookie stealing are the causes.
Securing the login using one of the methods suggested here puts a stop to that.
If you would like to explore the topic of WordPress security in more detail, you can view a 7-part article series here: https://www.kuketz-blog.de/basisschutz-wordpress-absichern-teil1/
In summary, maximizing security is no dark art - WordPress security for ambitious users - thanks primarily to NinjaFirewall.
- Details
- Last Updated: 22 March 2022