Website Malware Removal
On-demand WordPress and Joomla support
Has it happened to you too? Upset visitors inform you about a virus warning on your website. In more obvious cases, the homepage has been completely defaced, strange hacker messages appear on the screen, or visitors are redirected to dubious websites.
You can assume that a virus or malware is now spreading across your webspace.
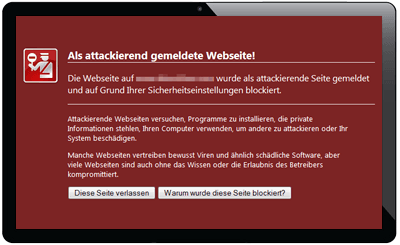
It often does not take long before Google itself and web browsers that rely on the Safe Browsing API warn potential visitors about your hacked website. Once Google is aware, visitor numbers drop sharply. Urgent action is required!
With many shared hosting providers, security is becoming more and more of a priority. As a result, temporary shutdowns to limit damage are not uncommon and are only lifted after cleanup and preventive measures have been completed.
Our services
- Error analysis & debugging
- Hardening
- Spam protection
- Updates & migrations
- CSS, JavaScript & PHP
- Customizations
- Speed Optimization
- Server migrations
- Statistics (Analytics & Matomo)
- Elementor
- Gutenberg
- Avada
- Divi
- WPBakery
- YOOtheme
- JoomShaper
- Forms
- Plugin consulting
- WooCommerce
- Appointment booking systems
- Newsletter
- Google Business Profiles
- Logo vectorization
- Plesk
- GDPR & cookie management
- Nextcloud
Current issue: Joomla Astroid Framework hacked - CVE-2026-21628
We are currently seeing an increasing number of inquiries about hacked Joomla websites using the popular Astroid Framework in use. The cause is a critical security vulnerability (CVE-2026-21628) in versions 2.0.0 to 3.3.10, which allows attackers to inject malicious code and leave backdoors behind. Updating to version 3.3.12+ closes the vulnerability, but it does not remove files that have already been injected, such as BLPayload or hidden SEO spam. We handle the complete cleanup and hardening of affected Joomla/Astroid websites. Learn more →
About - the story behind Website-Bereinigung.de
It all started in 2012 with the infection of around 40 websites we managed ourselves by a Trojan targeting FileZilla FTP credentials. Over the years, we have successfully completed more than 2000 cleanups (as of 2026) and gained extensive experience as a service provider in the fight against malware.
We want to use this knowledge to help you quickly and efficiently out of this difficult situation when it matters most.
Of course, it is not enough to simply restore all files to their original state. To avoid being hacked again just a few days later, the root cause must be identified.
On the one hand, viruses, malware, and similar threats can be injected directly into files through insecure passwords or stolen FTP credentials; on the other hand, outdated CMS and shop systems pose a major security risk. In these cases, we are dealing with classic hacks - the exploitation of security vulnerabilities. The best-known CMS in particular, such as Joomla, WordPressTYPO3 and Drupal are frequently targeted by attacks. Leading shop systems such as Magento, OXID, and xt-Commerce, including their forks, are also not spared.
When it comes to security, updates are the best form of prevention.